By default, most SIP devices use SIP over UDP as their main protocol, but for some enterprise unified communication scenario, it is required to deploy SIP over TLS to encrypt their communications. Cloud-miniSIPServer can permit users to connect their SIP phones or SIP clients to their virtual servers with SIP over TLS.
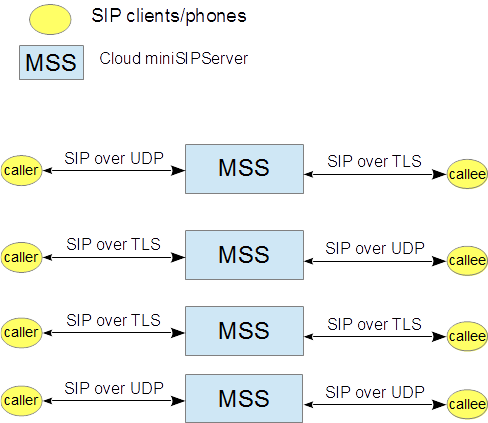
At this time, miniSIPServer can only permit local users (SIP phones) to be deployed with TLS. That means you can not configure "SIP server" or "External lines" with SIP over TLS
By default, miniSIPServer uses TLSv1.2 and TLSv1.3 methods. SSLv2, SSLv3, TLSv1 and TLSv1.1 have been discarded. Please make sure of your SIP phones can support TLSv1.2 or TLSv1.3.
You don't need to configure anything in your virtual server, please refer to following figure for this configuration.
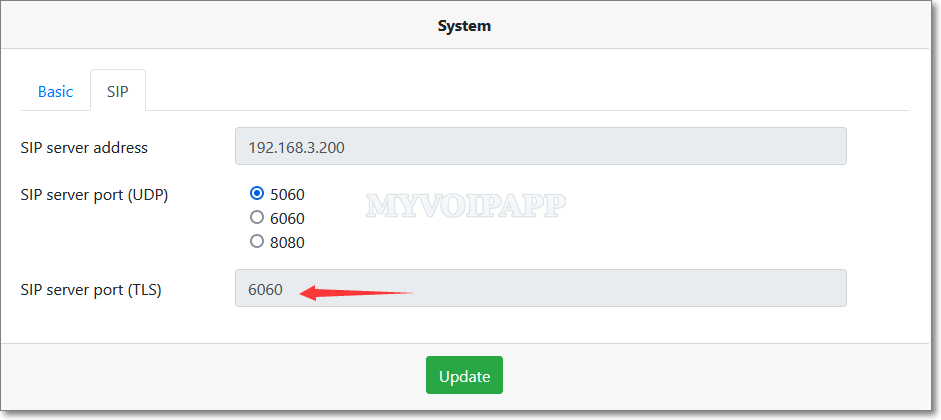
The SIP standard defines the TCP port 5061 to be the default port for SIP over TLS, but cloud miniSIPServer uses TCP port 6060 to accept or send SIP messages over TLS, you need to pay attention to it when you configure your SIP phones or SIP clients.
For example, you can configure miniSIPPhone as following:
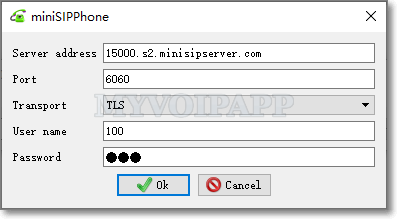
If your phones have an independent item to set server port, you can configure it to be 6060 directly.
In another way, we MUST configure its transport to be "TLS".
Q1. Why don't you use the standard TLS port 5061?
Since our cloud system is deployed in public network, it could be very dangerous to use the standard port. According to our experience, lots of scanner or hackers are scanning the standard port in public network. It could waste our resources to fight them, so using another port could be a simpler and better choice.
Q2. Can I configure another TLS port?
No, you can't. At this time, we only open TCP port 6060 to accept SIP messages over TLS.